Is it really that bad to use the same password everywhere?
The fact that 50% of business passwords can be cracked within a few minutes is deeply disturbing and yet, even though business owners are becoming more aware of the threat of weak passwords in the workplace, there’s a belief that a password is acceptable simply if it has fulfilled the minimum requirements for a password.
But life is not that simple…
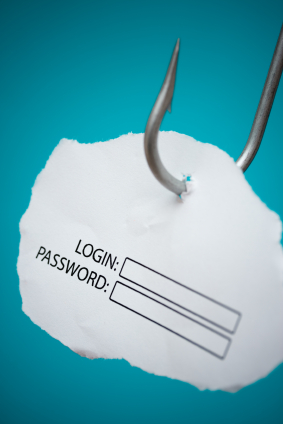
How passwords are stolen

Hackers target passwords at both the user end (e.g. via phishing emails containing links to malware that can log keystrokes, or social engineering methods that use third party information to guess passwords) and at the destination (e.g. the malware infections at Target in 2013, and Home Depot this year, which accessed user data before it was encrypted).
But it’s not just clever malware that’s to blame. Adobe’s breach in 2013 was the result of a weak security practice: although user passwords were encrypted, the password hints were not, thus opening the door to any enterprising hacker with a penchant for problem-solving.
It means that even if a user creates a super-strong password, there are still points in the data chain that may be weak enough to allow a security breach.
Hack one, get one free
Unfortunately, one successful hack is typically the start of a chain reaction, where stolen passwords from one account are tested more widely in the expectation that they will gain access to another account.
This happened when stolen LinkedIn details were used by hackers to gain access to Dropbox accounts. Accusations of fault on the part of Dropbox were unfounded – hackers simply had success with the passwords they had procured elsewhere.
In another case, 5 million Gmail account names and passwords were stolen and uploaded to a Russian Bitcoin forum. When WordPress ran this leaked list against their own massive database, there were 100,000 cases of exact match on account name and password, each one of them a potential hacking opportunity.
Exponential risk
Despite hugely publicised breaches such as these, over 50% of internet users still use the same password on multiple sites which, by definition, puts multiple parties at risk: the user, plus all businesses where the same password is being used. And the downstream ripple is compounded.
So, if your employees use the same password in the workplace as they do on other accounts then, no matter how strong the password, they are effectively providing an interface between those systems. The result is a security gap just waiting to be breached.
Any raid could potentially harvest not only your company’s resources but the next pool of passwords to be tested on other business networks.
How to stop the snowball
Whilst the danger of employees using passwords in multiple places remains a significant threat to all businesses they interact with, business owners can implement some simple measures to stop this type of snowball, or domino effect, cybercrime.
Firstly, make sure that employees use strong passwords on all accounts, both personal and business. Strong passwords are those that are, first and foremost, long and which contain a mixture of upper and lower case letters, as well as special characters. Password management software is the best option for storing these hard-to-remember, hard-to-crack passwords.
Secondly, a formal security policy should be established: in terms of password security, make it mandatory that they cannot be used elsewhere, either internally or externally.
Finally, keep abreast of external security breaches as a result of password hacks and use them to reinforce correct behaviour in your own business.
One account, one password
Shared passwords are like skeleton keys and - like any other common thief - hackers love them. If a strength meter takes a password part of the way in defeating them, it’s up to users to do the rest: one account, one password.
Related Articles
Why are we still using passwords in 2022?
With Verizon reporting that 82% of data breaches involved the Human Element, why are businesses still using passwords and putting their security and reputation in...The 3 Steps to Passwordless
More than 80% of all enterprise data breaches are made possible by weak or stolen passwords. The majority of employees who have already been scammed through...Identity and Access Management for Web, Mobile and Windows Desktop Applications
Identity and Access Management for Web, Mobile and Windows Desktop Applications










-
© My1Login 2007 - 2024
- Terms & Conditions
- Anti-Slavery Policy
- Back to the top ↑
